Prerequisites –
Users should have the “CC full access” permission set assigned.
Procedure:
To create a Data Retention Rule, you’ll need to go to the ‘Implement’ tab.
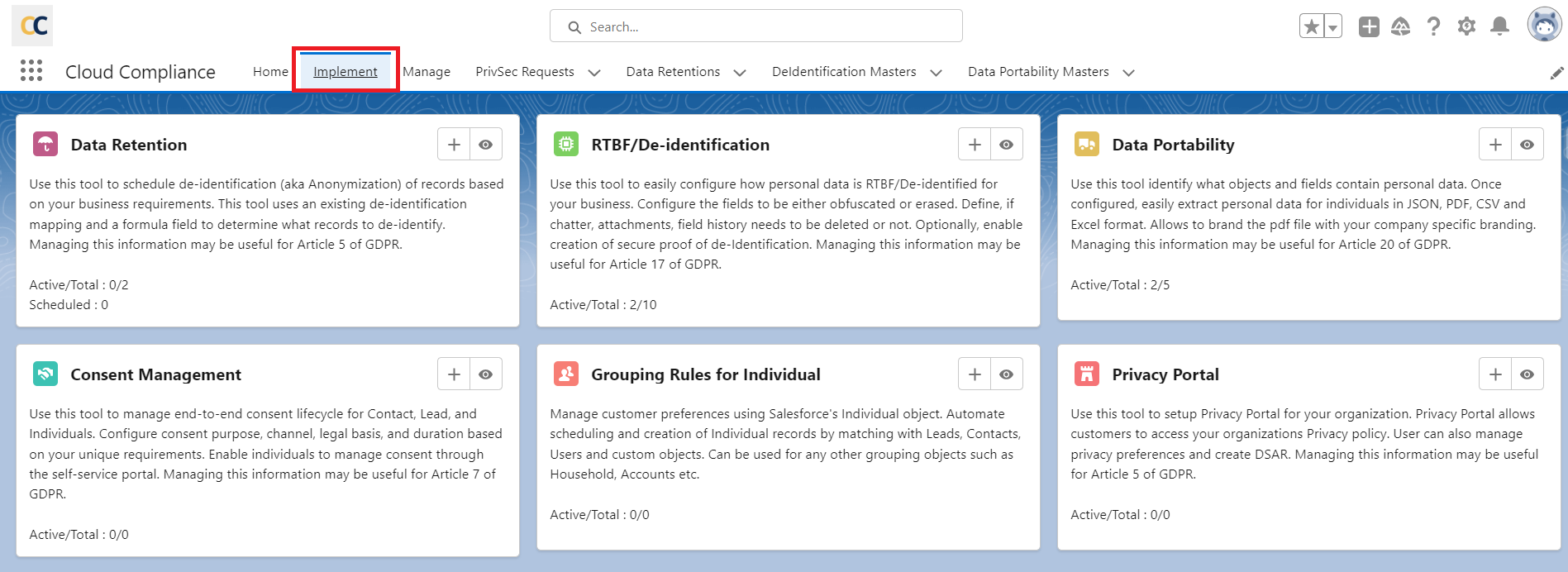
Click on the ‘Add’ button
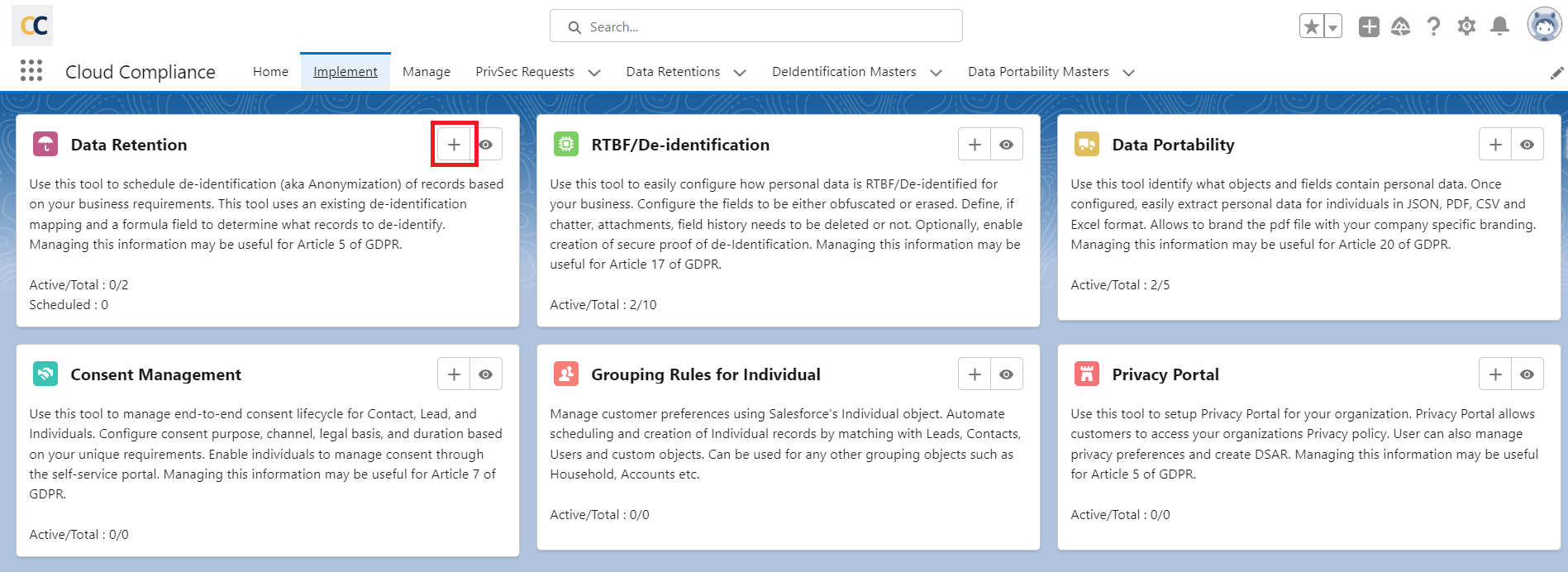
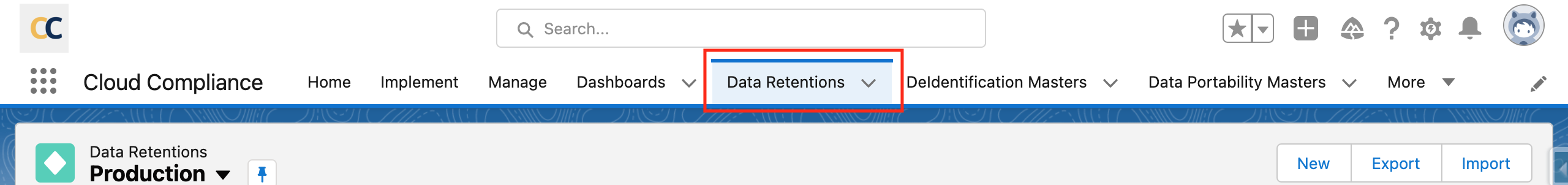
Step 1: Navigate to the Data Retention Tab
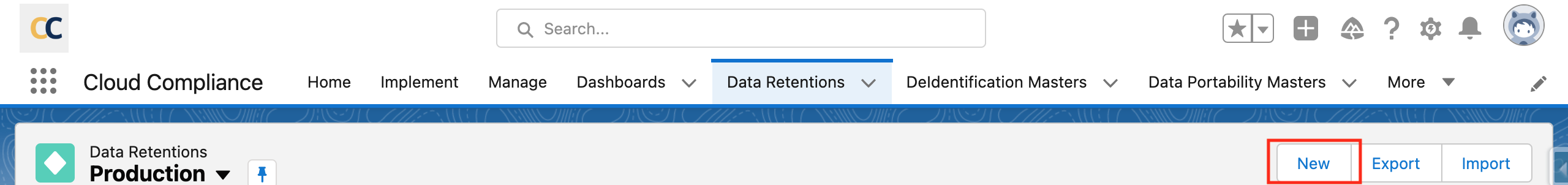
Click on ‘New’ to create the Data Retention rule.
Step 2: Fill in the respective fields.
Here users will see some fields that need to be filled, the significance of each field is given below.
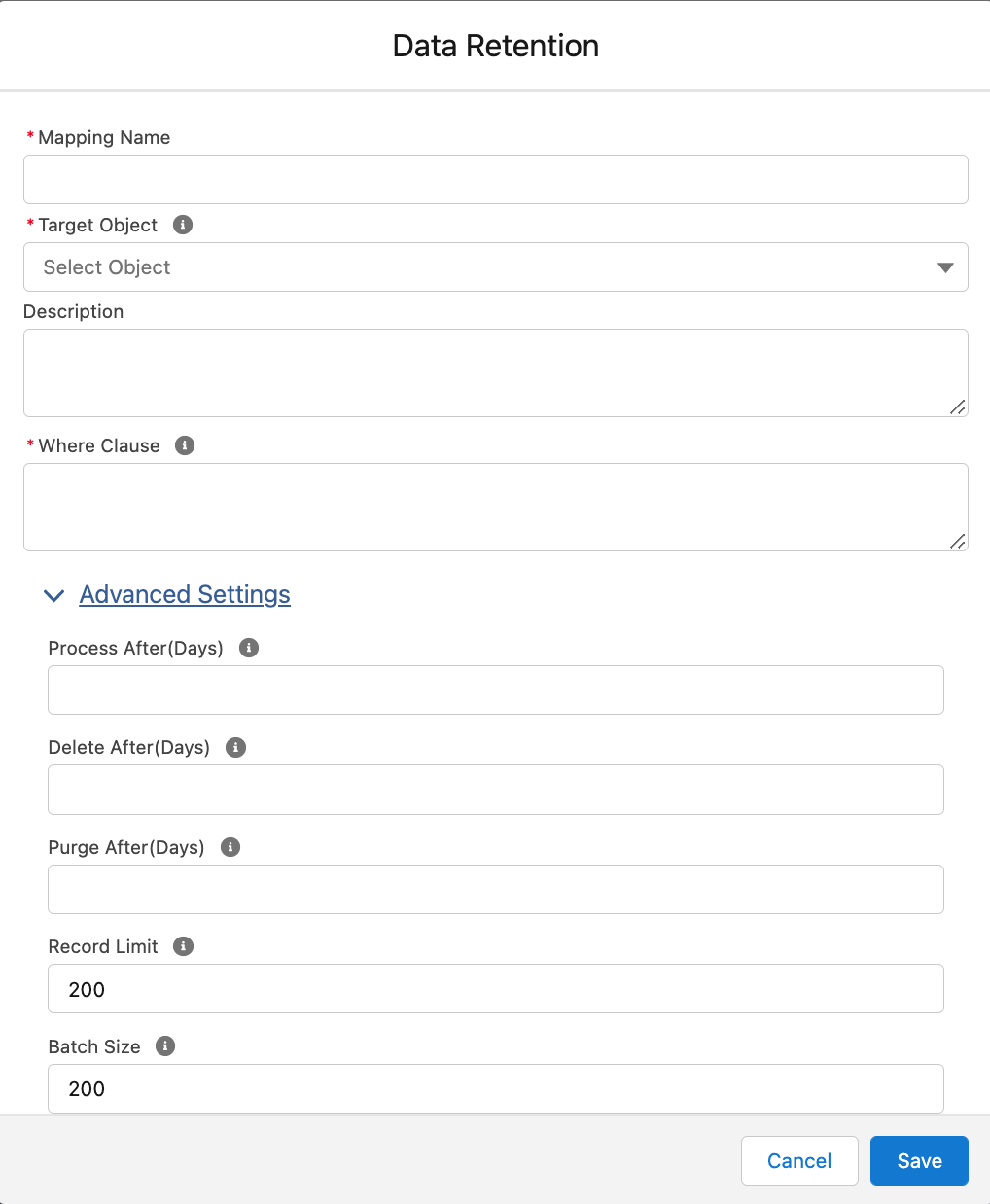
Mapping Name – Give the name for the Data Retention Mapping
Target Object – In the “Target Object” field, you can select the object for which you want to perform data retention.
Description – In the “Description” field, you can add any description related to the process. This is an optional field.
Where Clause – The “Where Clause” field allows you to filter records for De-identification dynamically and on the basis of cross-object values.
Process After (Days) – The “Process After (Days)” field triggers the Retention/RTBF process on the mentioned day. If you leave it blank, then it will be considered as a value of 0 days so that the processing date will be considered as today’s date on the PrivSec Request Record.
Delete After (Days) – The “Delete After (Days)” field triggers the deletion batch to delete all of the records which are de-identified. If you leave this field blank, then no deletion date will be considered on the PrivSec Request record, and the records will remain in the org even after the De-identification process. This value should be greater than or equal to 1 but can not be Zero.
Purge After (Days) – This “Purge After (Days)” field triggers the purge records batch to delete all the Associated Records corresponding to de-identified records. If the user keeps this field blank, then no purge date will be considered on the PrivSec Request record and the associated records will remain in the org even after the De-identification process is completed.
Record Limit – The “Record Limit” field divides the PrivSec Request record depending upon the Record Limit mentioned. For example, if the Record Limit is set at 20 and if we follow the Retention Rule, there are 100 qualified Contacts, then 5 PrivSec Request records will be created to avoid Record Locking issues.
Batch Size – The “Batch Size” field decides how many records will be processed in a single batch. For example, if the Batch Size is 2000, then 2000 records will be processed in a single batch.
In the case of User Obfuscation, the Batch Size should be 175, when Data Retention User mapping is with or without the checkbox of ‘Use Standard User Obfuscation’.
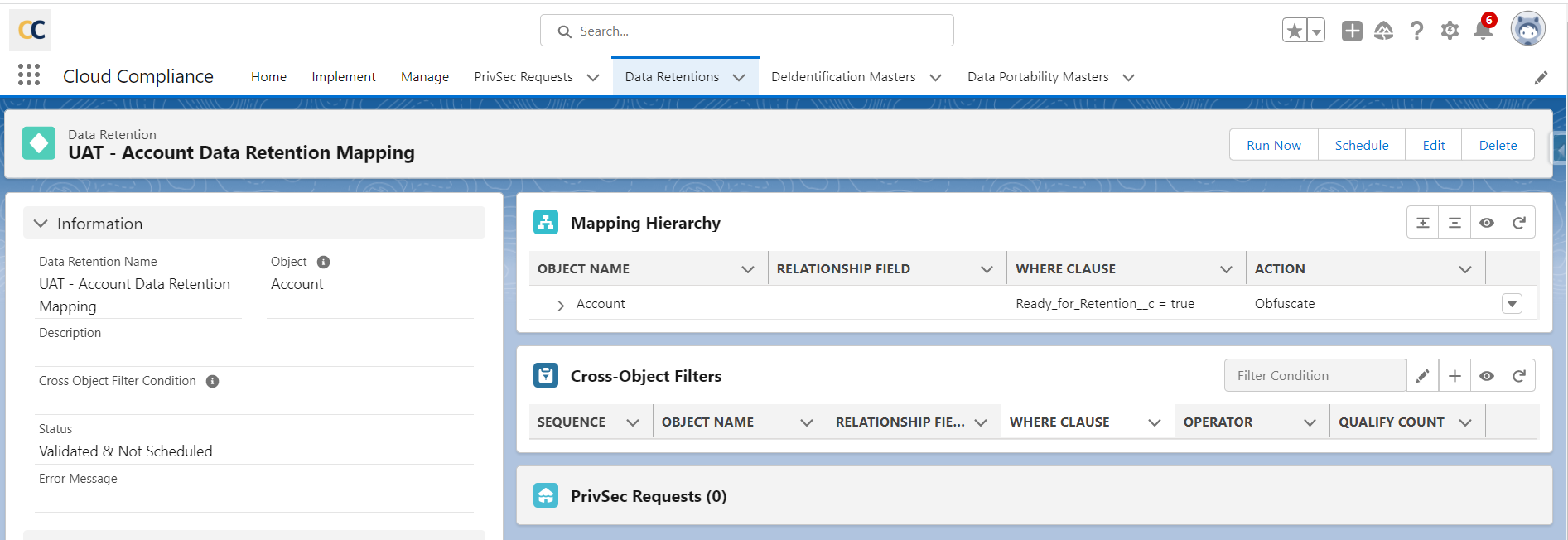
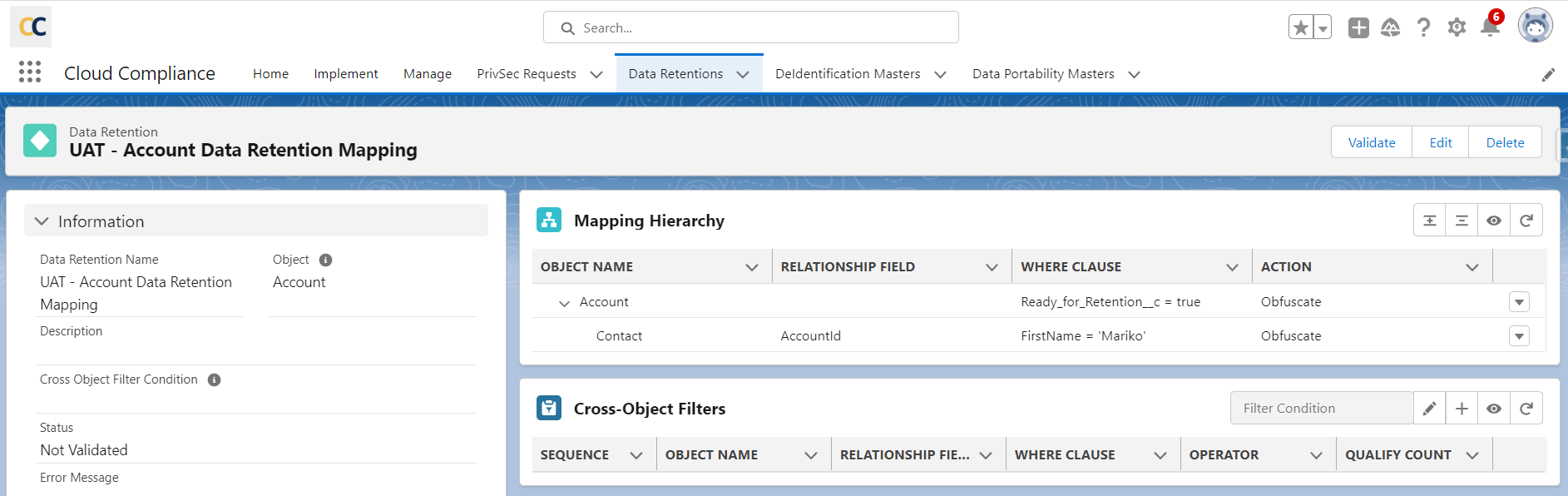
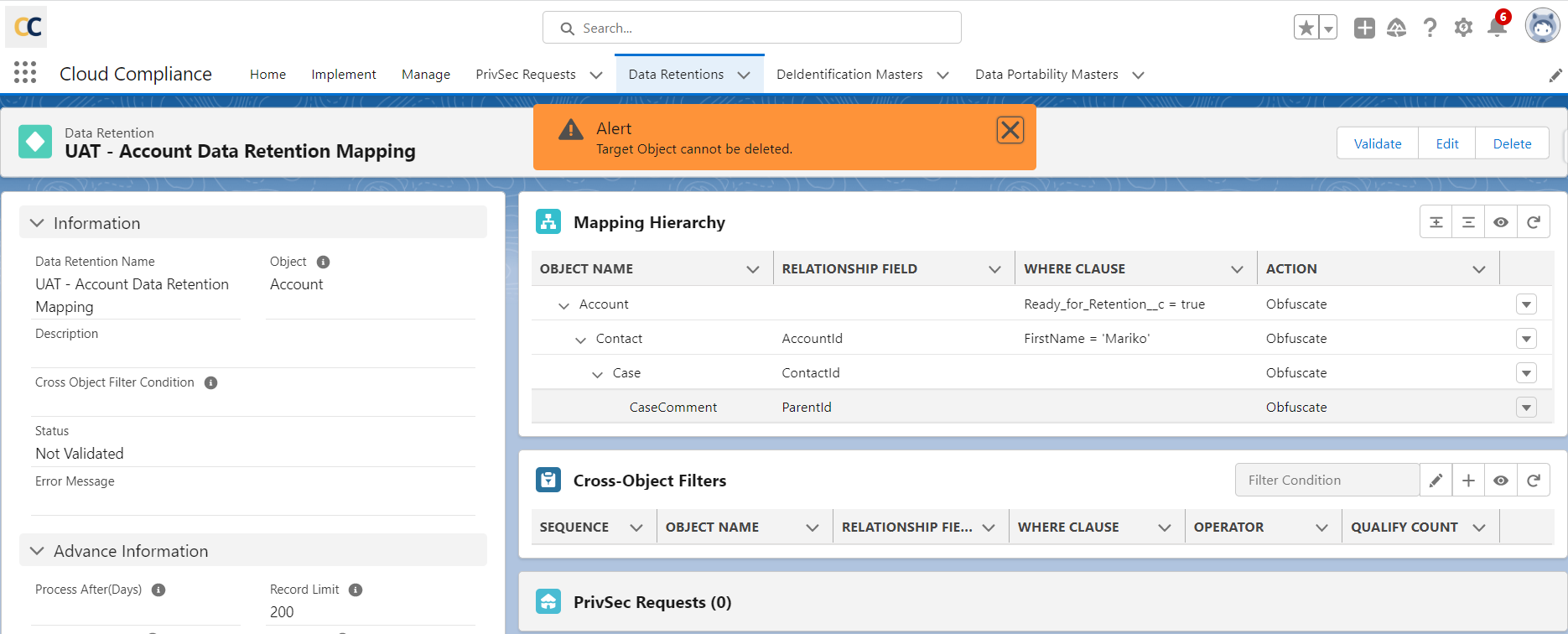
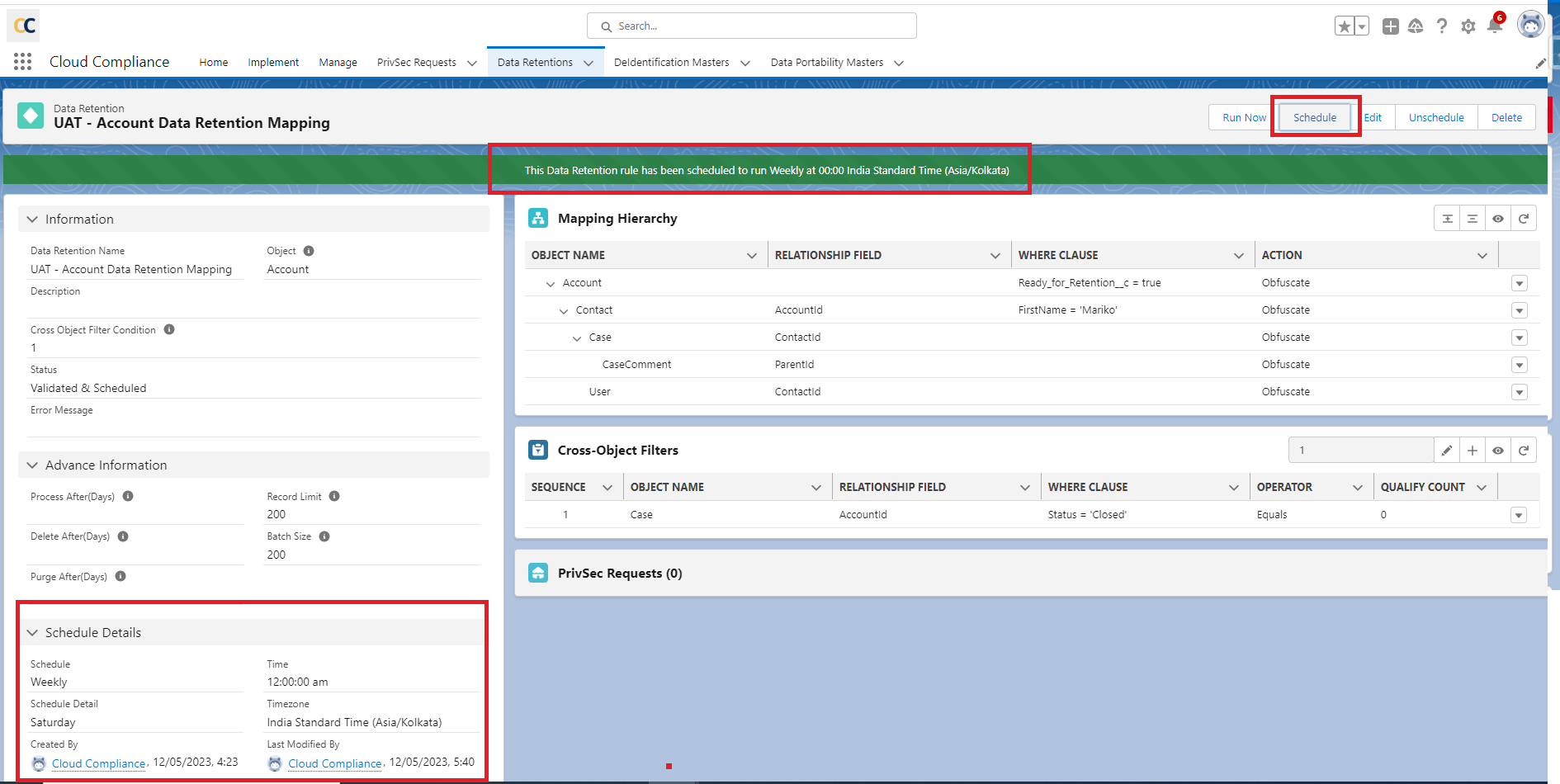
When you set the criteria as ‘Ready_for_Retention__c = true’ in the ‘Where Clause’ as shown in the above image, the retention batch will fetch only those records whose ‘Ready for Retention’ checkbox on the Account object record is checked, and will process these records accordingly.
Suppose the Account object has some child objects and the user needs to de-identify the records of child objects too. In that case, the user can add that object to the Data Retention mapping allowing it to properly pick and process the records as per the Data Retention Mapping structure.
Click ‘Save’
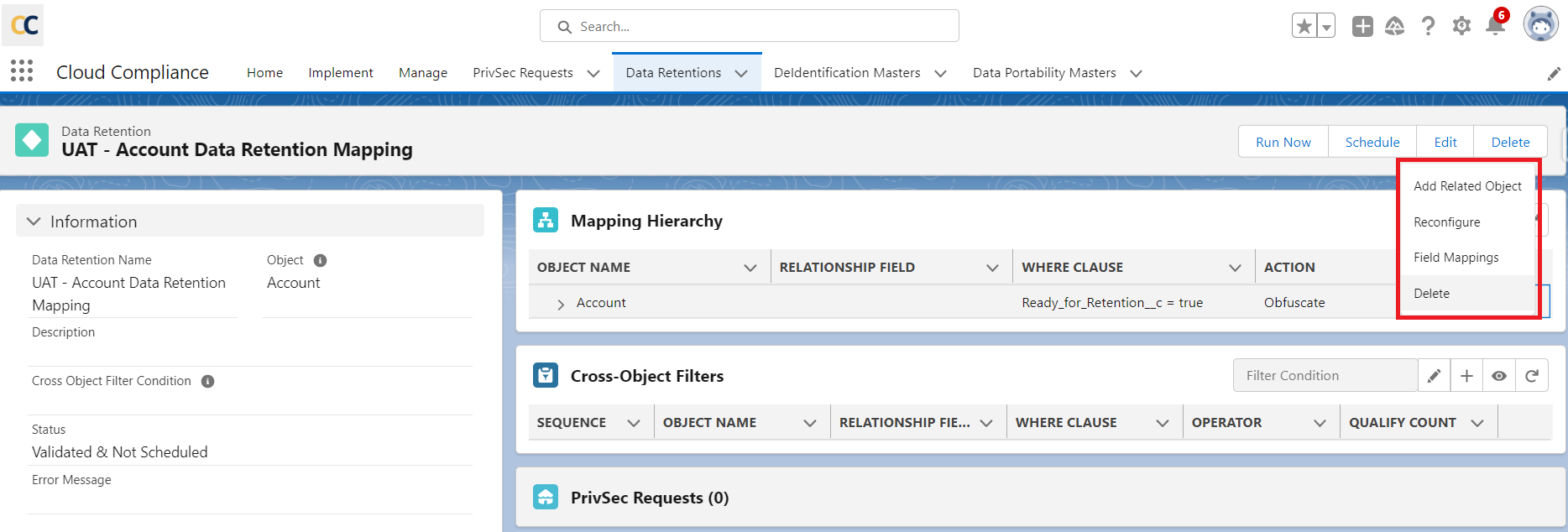
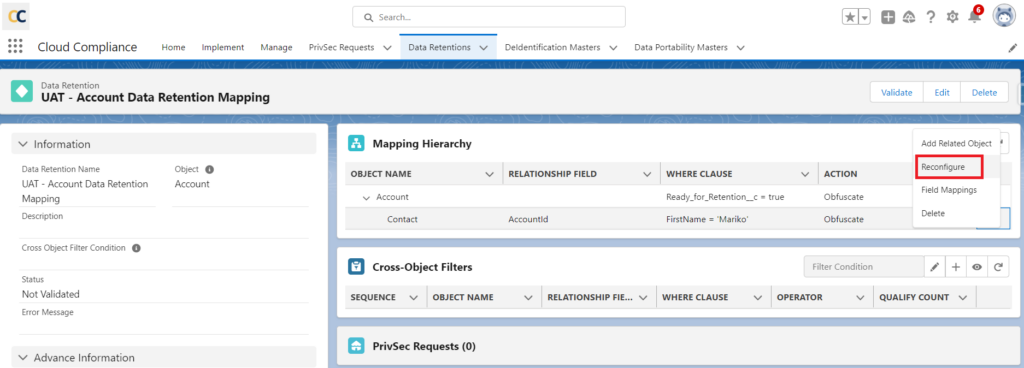
- Click on the dropdown arrow, the user will see four options
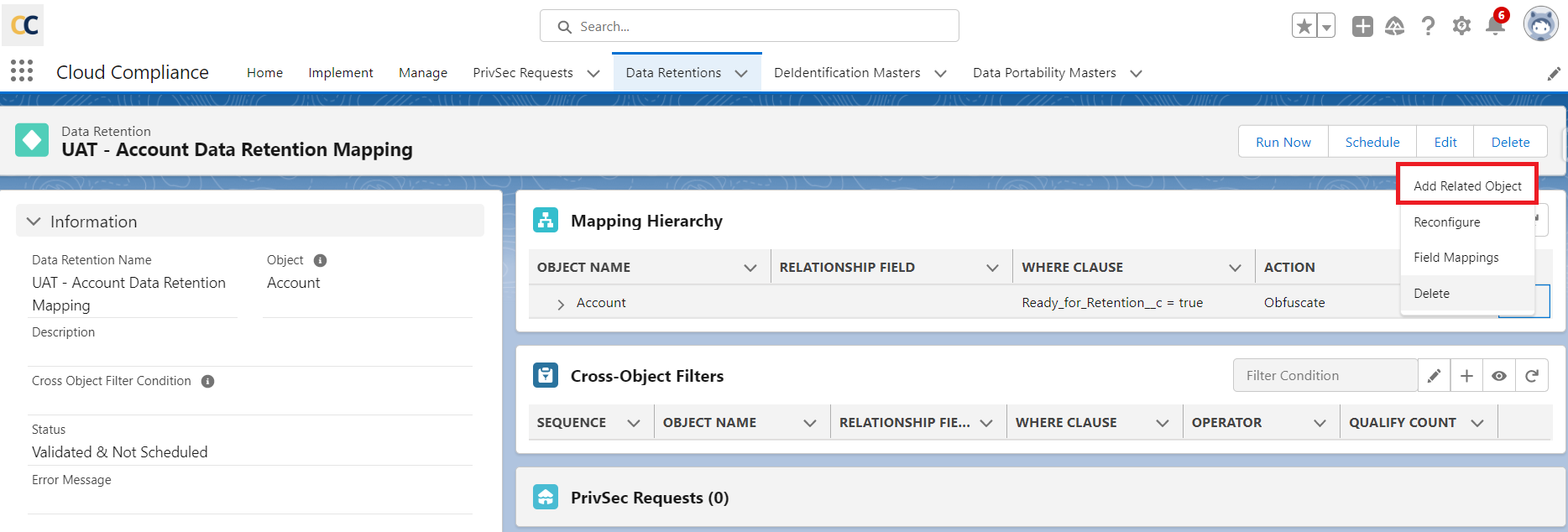
1. Add a Related Object
2. Reconfigure
3. Field Mappings
4. Delete
Add Related Object – After clicking on this user will be able to add a related object under the parent object.
All the child objects of the selected object (We have taken Account Object as a parent object here) will be shown in the list as shown below
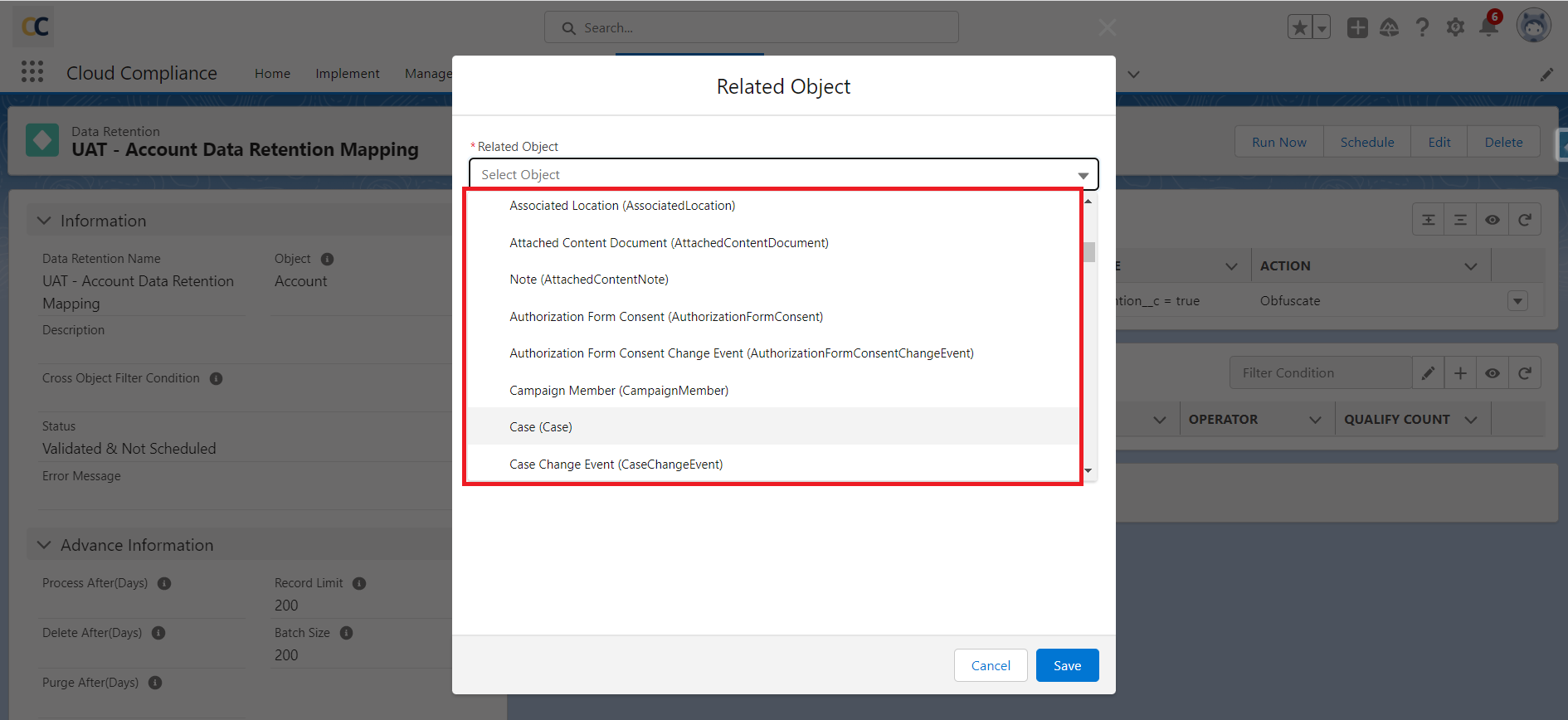
Relationship field –
- When we create a mapping for a child we have to assign the relationship field so that the application can understand the path it has to take.
- After selecting the child object the relationship field between the parent and child object will be populated automatically.
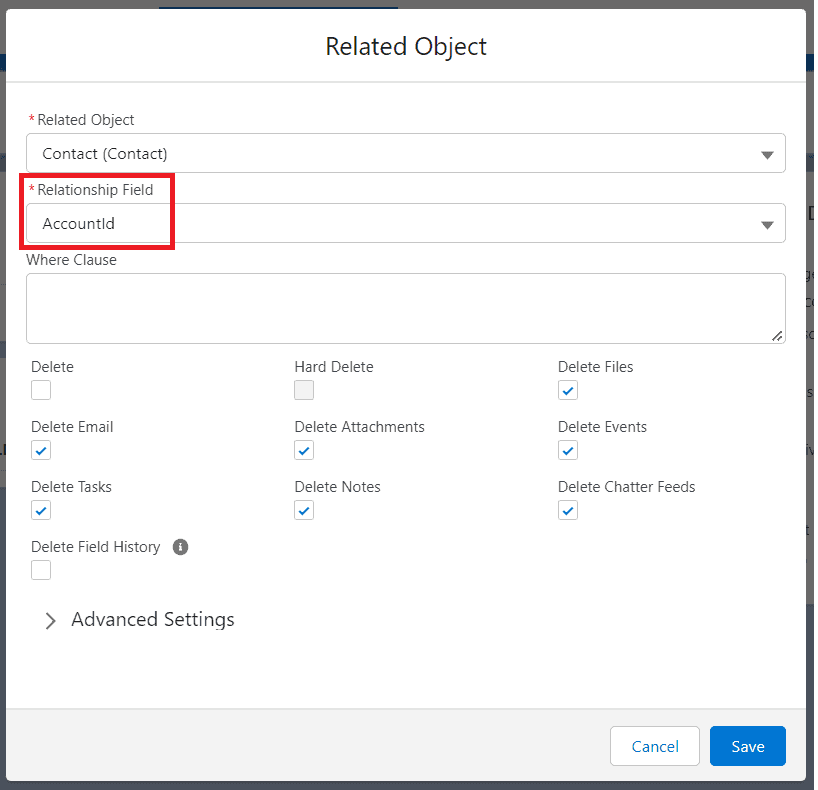
If there are multiple relationship fields, the user can select from the drop-down list of ‘Relationship Fields’
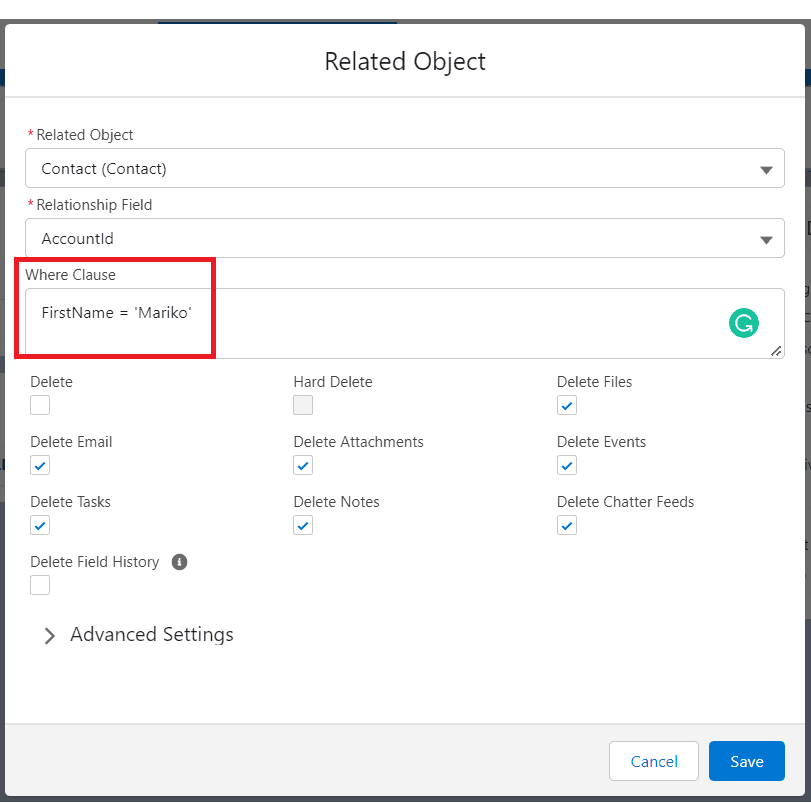
Filter Field- Filter records by entering a WHERE clause and the filter field should be like FirstName = ‘Mariko’ hence Retention will be performed only on those records where FirstName = ‘Mariko’ as shown in the below screenshot
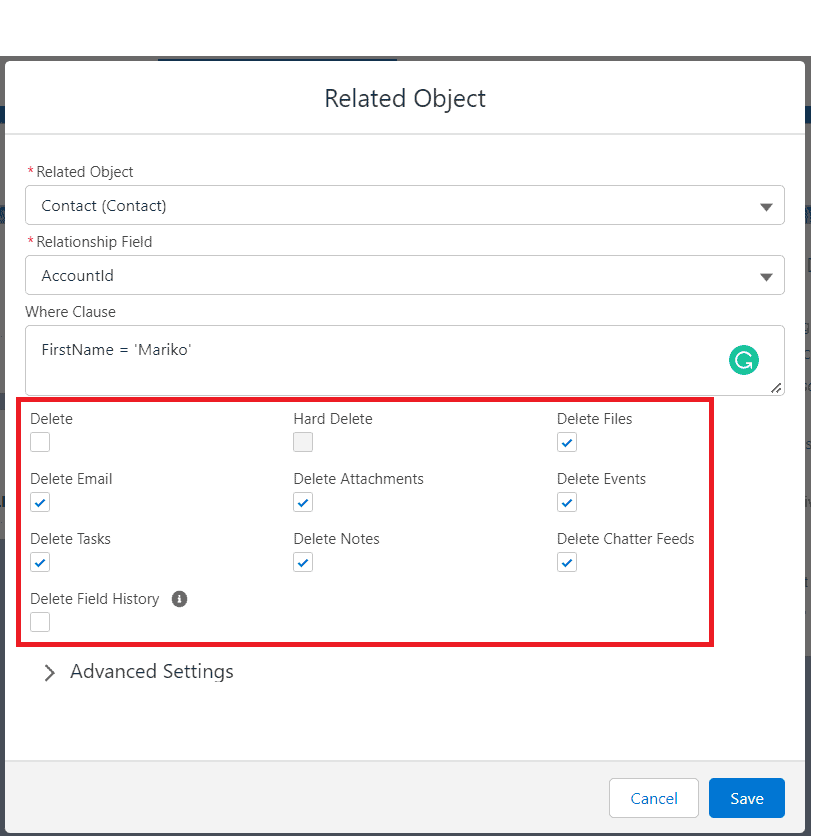
SETTINGS :
Delete- Data Deletion allows users to delete any number of records attached to the objects in the hierarchy mapped.
Hard Delete- Data Deletion allows users to permanently delete any number of records attached to the objects in the hierarchy mapped.
- Delete Attachments: It allows users to delete the attachments related to the de-identified record.
- Delete chatter feeds: It allows users to delete the chatter feeds related to the de-identified record.
- Delete Events: It allows users to delete the events related to the de-identified record.
- Delete Notes: It allows users to delete the notes related to the de-identified record.
- Delete Tasks: It allows users to delete the tasks related to the de-identified record.
- Delete Emails: It allows users to delete the Email activities related to the de-identified record.
- Delete Files: It allows users to delete or de-link the files which are related to the de-identified record.
Note: If the file is shared exclusively then that file will get deleted permanently from the de-identified record and if the same file is shared with two or more different records then the file will get delinked from a de-identified record and remains as it is with the second record. - Click on the Save button.
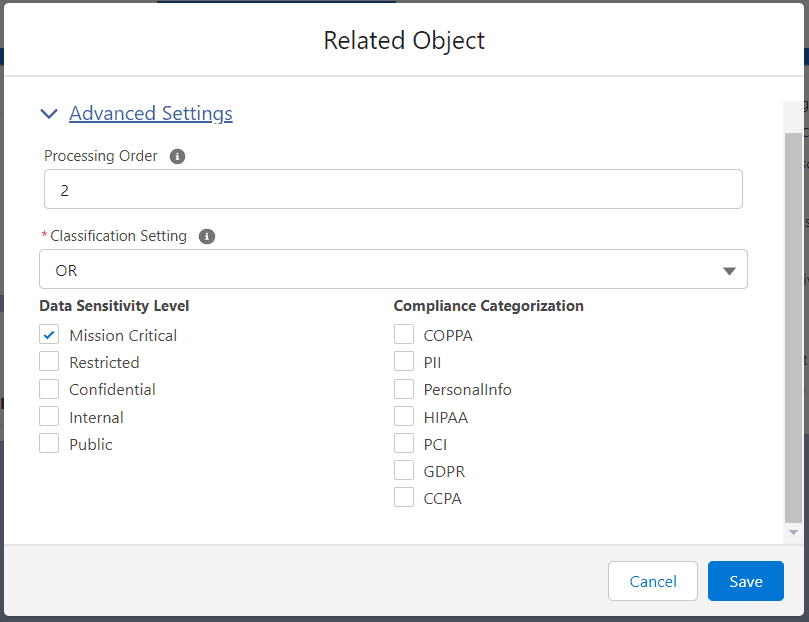
Advanced Setting :
When the user clicks on Advanced Settings, It will expand and show Processing Order and Classification Settings.
A. Processing Order: This functionality simplifies the processing of parent and related objects by allowing you to decide your own sequence within RTBF / Retention Mapping. You can leave this field ‘Blank’ to process the execution of other related objects after the sequence. This field enables the user to insert a sequence of integers, ranging from 0-99.
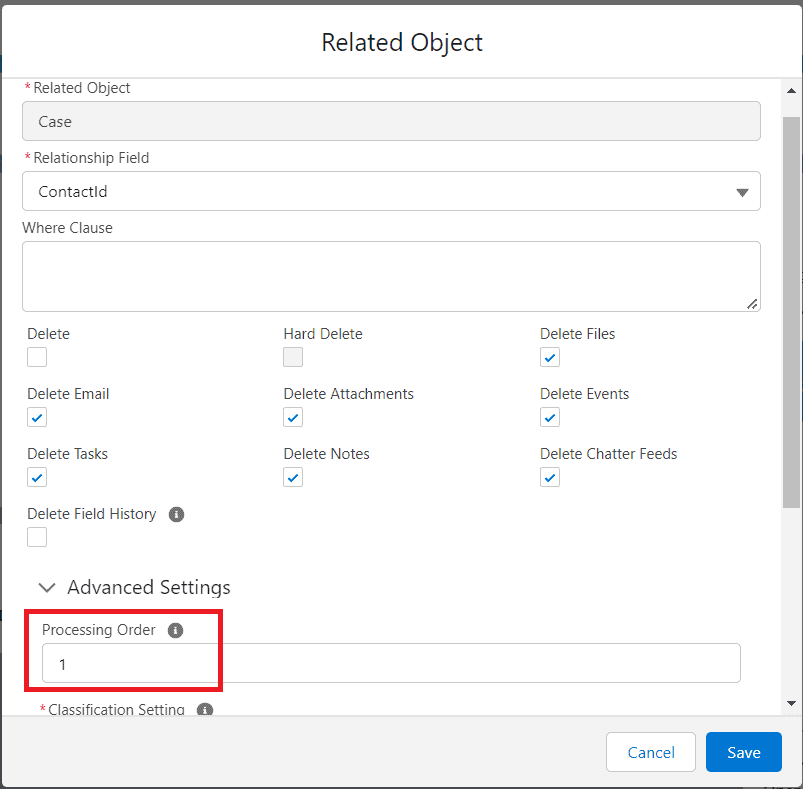
- For Example, If the Account is a parent and the Case is a child of the Account, the processing order for the case is 1, and the processing order for the account is 2.
- As per the processing order, the Case will be processed first for the Obfuscation/Deletion, and after that Account will be processed.
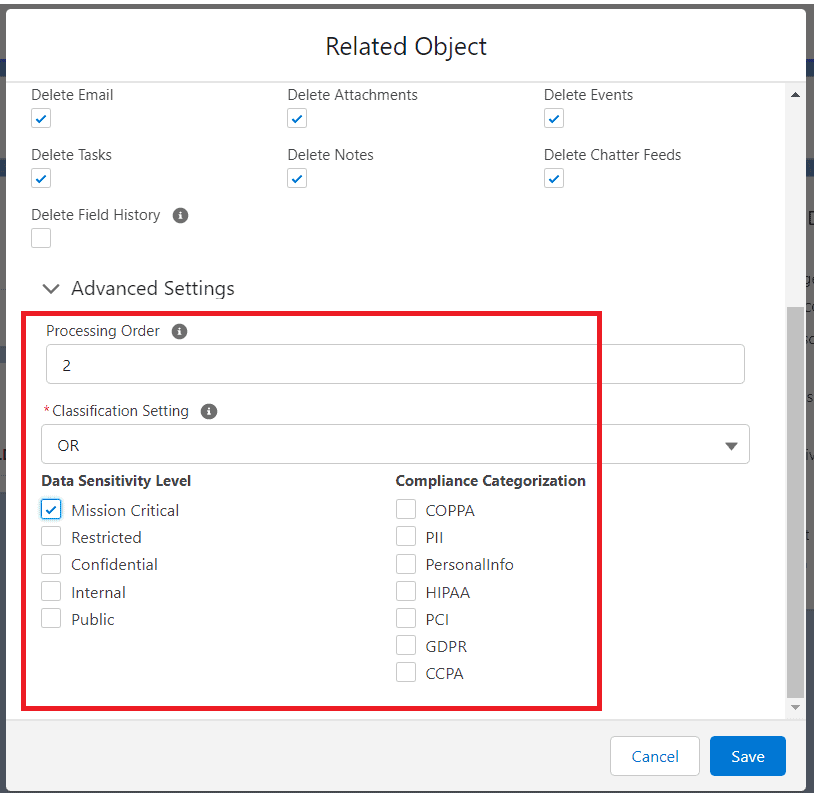
B. Classification Settings :
- Data Classification enables users to classify the data as per the Data Sensitivity Level. Users can decide which data is to be De-identified and which is not.
- To process the records as per Data Classification user needs to add the Data Sensitivity Level to the fields of an object.
- This functionality has been introduced in CC 2.29 version and onward.
- Users can see the Data Classification section on the De-identification mapping page as shown in the below screenshot.
- Note – To enable Data Classification functionality, follow the below path –
Setup -> Installed Package -> Configure -> De-identification -> Data Classification -> Enable Data Classification
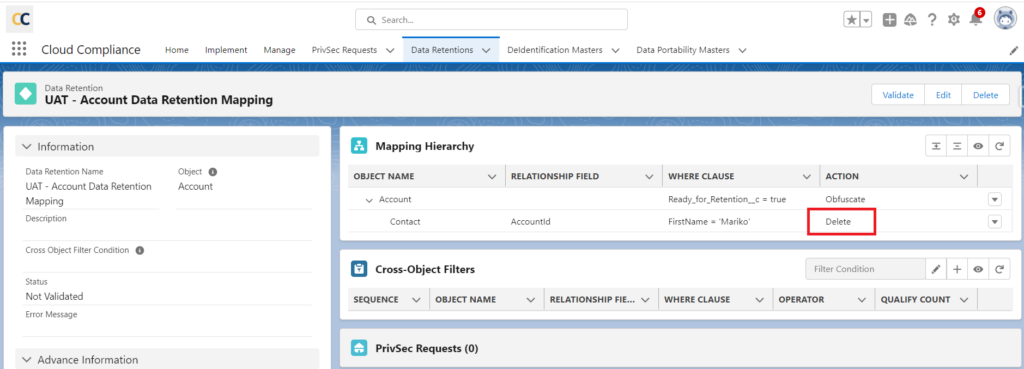
2. Reconfigure – After clicking on Reconfigure user will see two sections of settings shown below
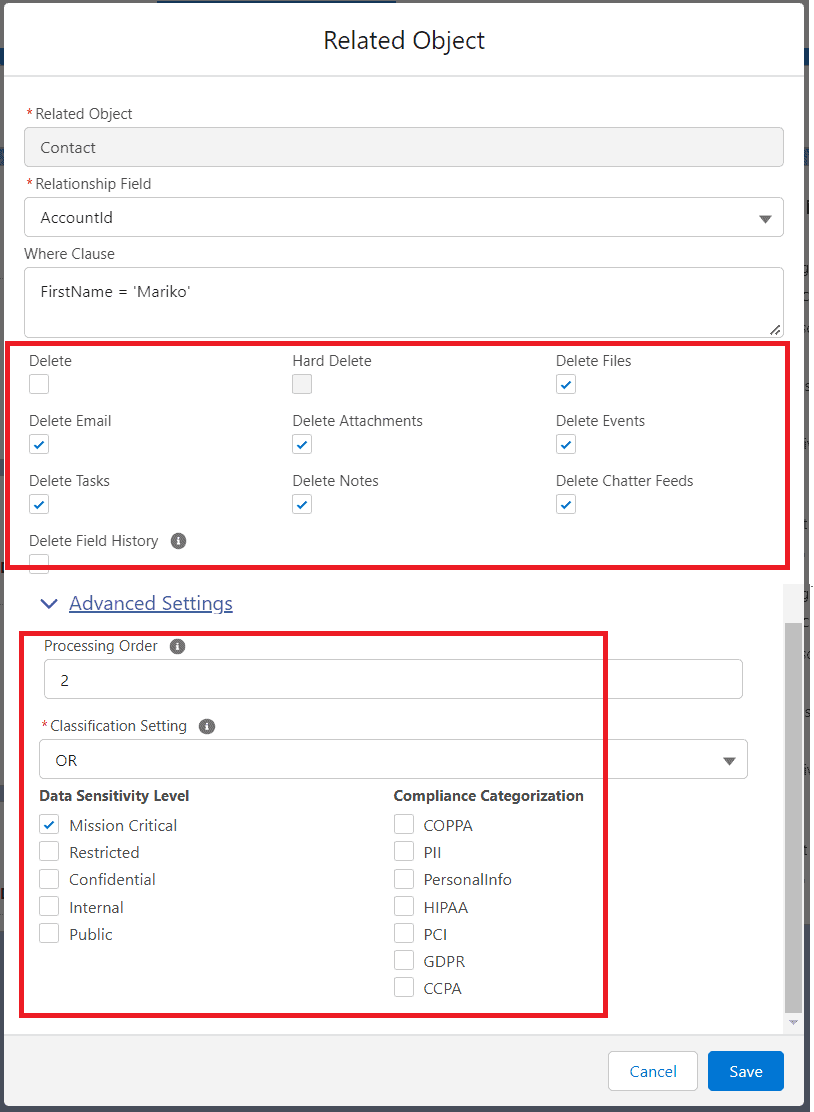
Delete Settings -In this section user can select Delete activities like Tasks, Notes, Attachments, etc. as mentioned above.
Users can also select the ‘Delete’ checkbox which will Delete whole records of the objects
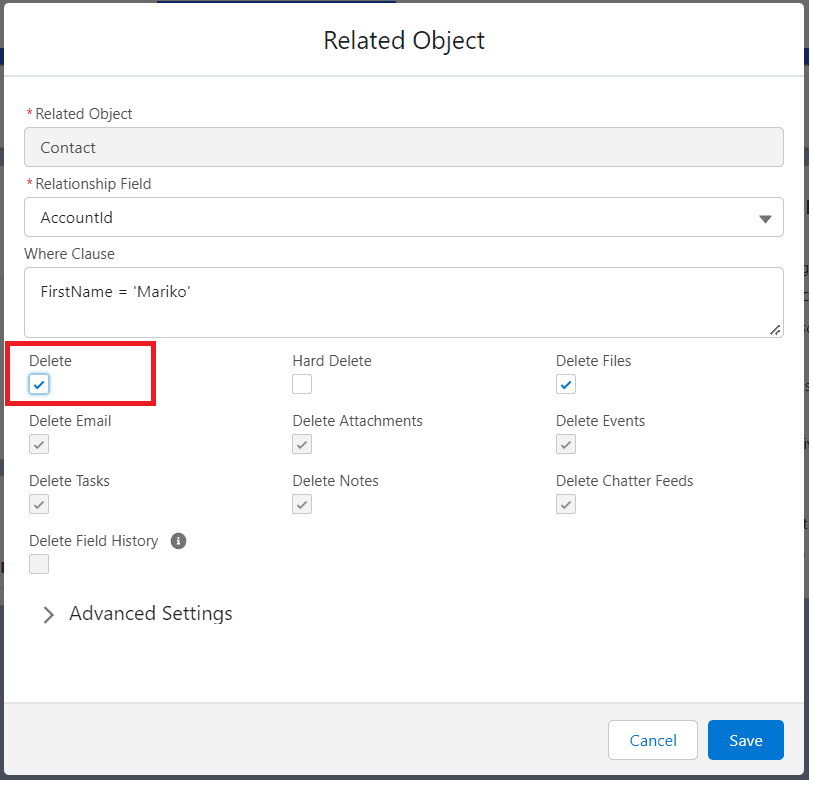
After clicking on the save button user will see the Action ‘Delete’ for the object.
Classification Settings – The user can De-identify the Object records as per the Data Classification and Data Sensitivity Level.
- Data Sensitivity Level
Users can add the filter based on the Data Sensitivity Level so that CC will check the Data sensitivity level of the field for the record that the user wants to do RTBF/Retention on.
- Compliance Category
The compliance acts, definitions, or regulations that are related to the field’s data.
Default values:
CCPA—California Consumer Privacy Act
COPPA—Children’s Online Privacy Protection Act
GDPR—General Data Protection Regulation
HIPAA—Health Insurance Portability and Accountability Act
PCI—Payment Card Industry
PersonalInfo—Personal information.
For use with the Enhanced Personal Information Management feature. Only available if Enhanced Personal Information Management and Digital Experiences are enabled.
PII—Personally Identifiable Information
The field corresponds to the ComplianceGroup field on the FieldDefinition Tooling
API.
Data Classification works with AND and OR conditions to achieve Data Classification
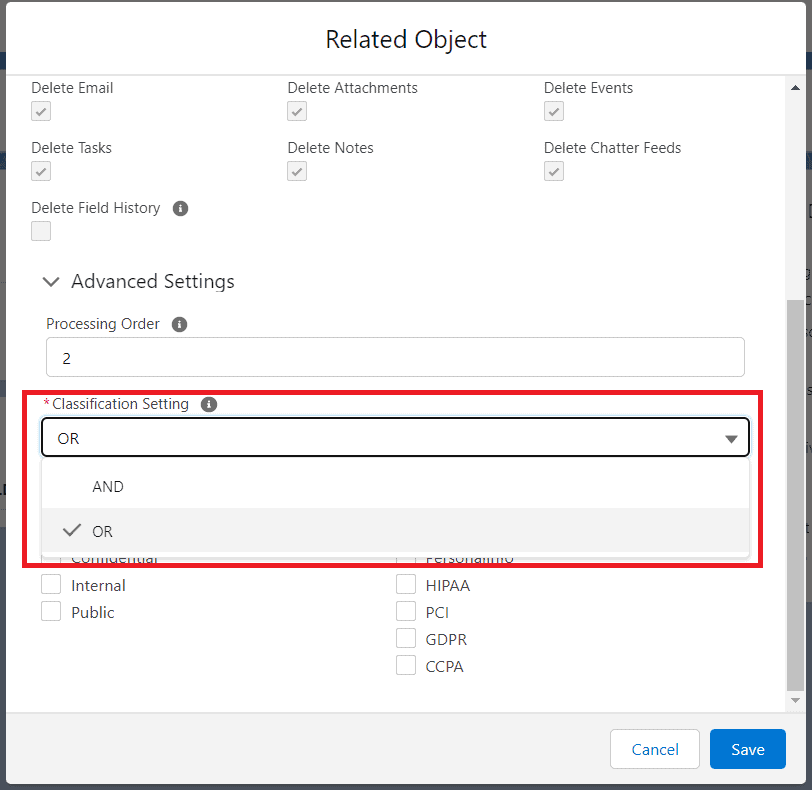
The records that satisfy the Classification criteria those only records will be picked and processed.
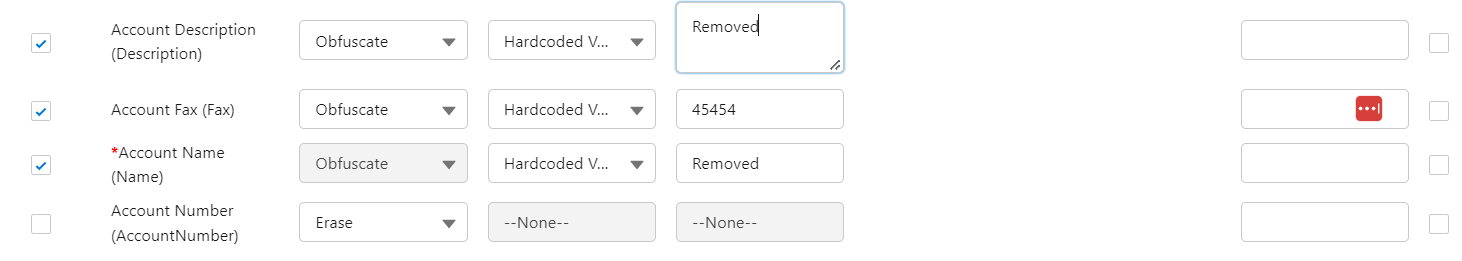
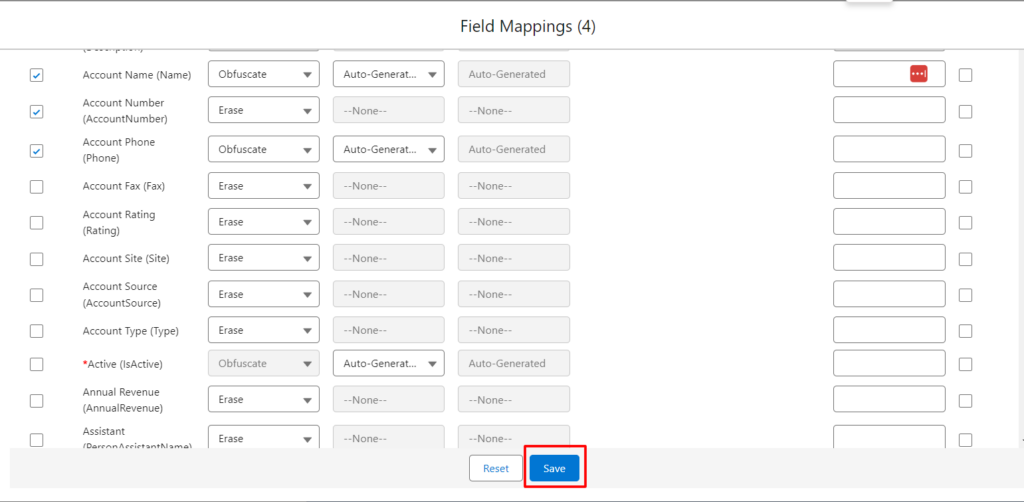
- Field Mappings – Here, the user can add field mapping for an object. After Clicking on Field Mappings user will see all the updatable fields for the De-identification pro
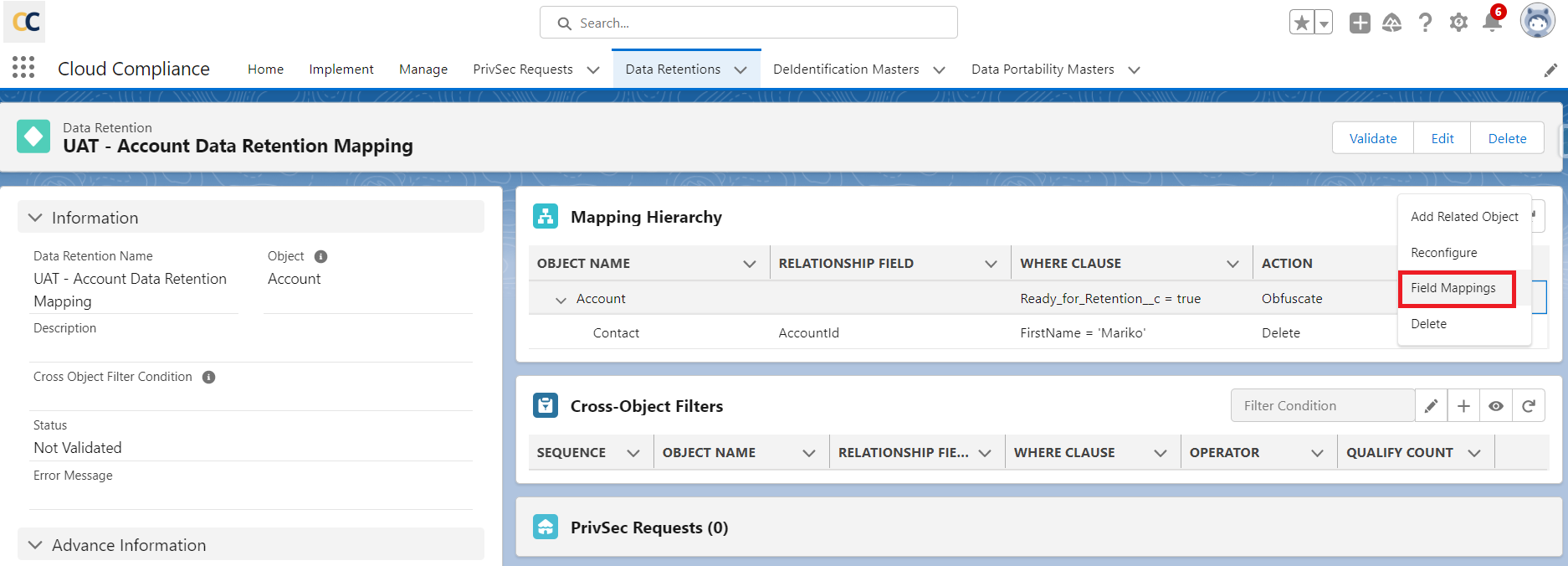
Click on the Field Mappings. Popup appears.
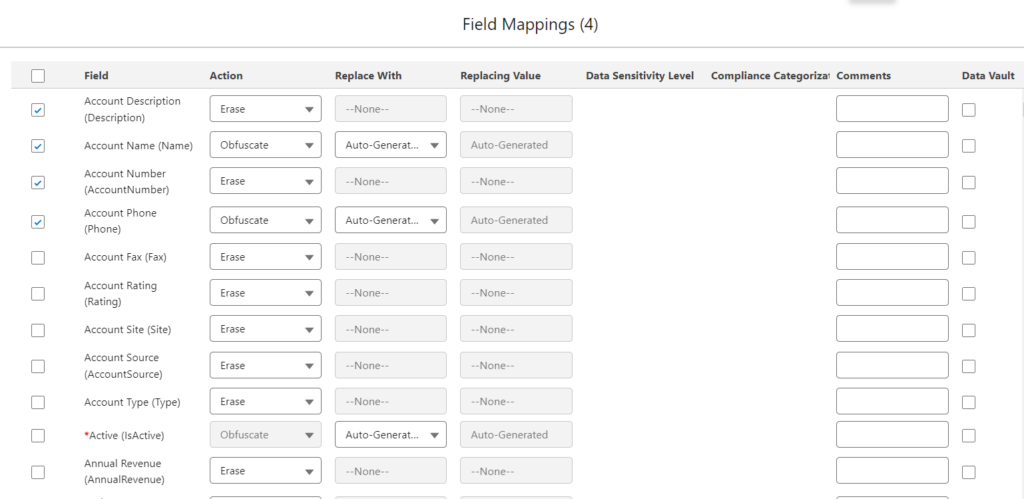
Select the field for RTBF by checking the checkbox.
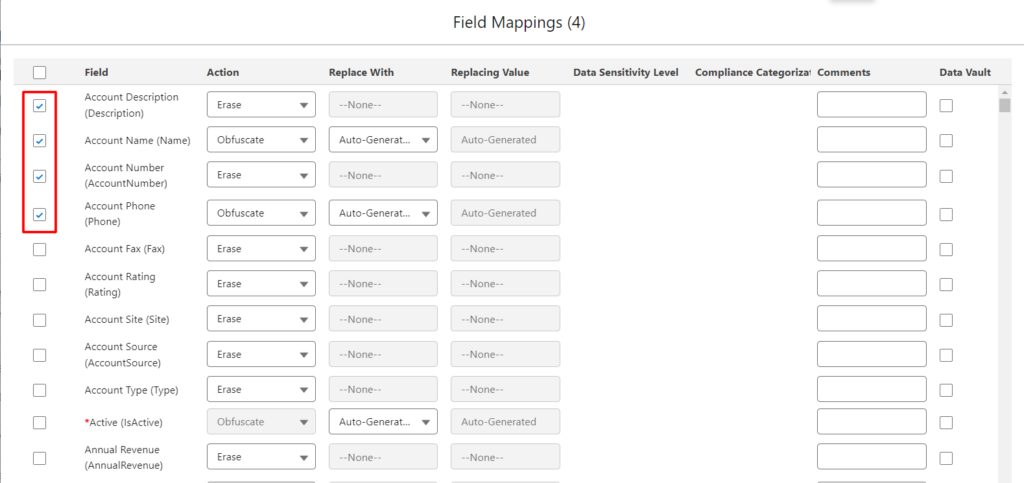
There are 3 different ways a user can replace the original text.
Auto-Generated
Formula Field
Hardcoded Value
- Auto-Generated – In this obfuscate action, the field value will be replaced by randomly generated scramble data. To achieve this obfuscation, keep the ‘Replace With’ field value as it is i.e To ‘Auto-Generated’.
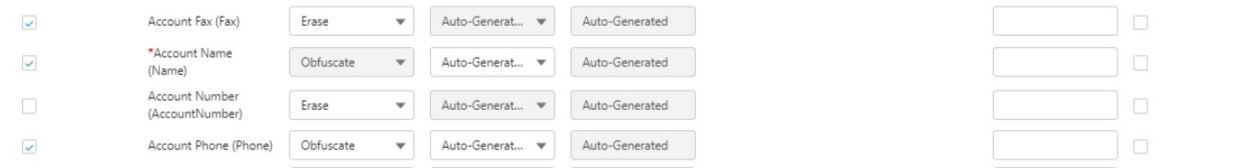
2. Formula Field – Another special feature of Obfuscation is replacing the field value with the formula field value.-
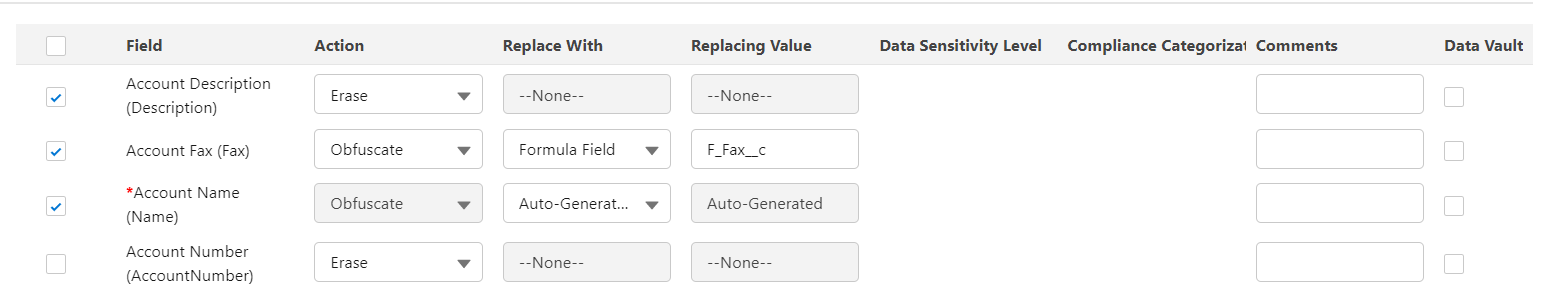
3. Hardcoded Value -Obfuscation also supports replacing field values with hard-coded values. To achieve obfuscation using a hardcoded value write the hardcoded value in the section ‘Replace With’.E.g. Removed.
- Data Sensitivity Level
Users can add the filter based on the Data Sensitivity Level so that CC will check the Data sensitivity level of the field for the record that the user wants to do RTBF on.
- Compliance Category
The compliance acts, definitions, or regulations that are related to the field’s data.
Default values:
CCPA, COPPA, GDPR, HIPAA, PCI, PII
- Comments
In the Comments section, users can add any additional information if required.
- Add to Data Vault
If a user wants to store the proof of de-identification then the user needs to select the ‘Add to Data Vault’ option.
Save the mapping.
4. Delete – After Clicking on the Delete button user can delete the selected object from the mapping.
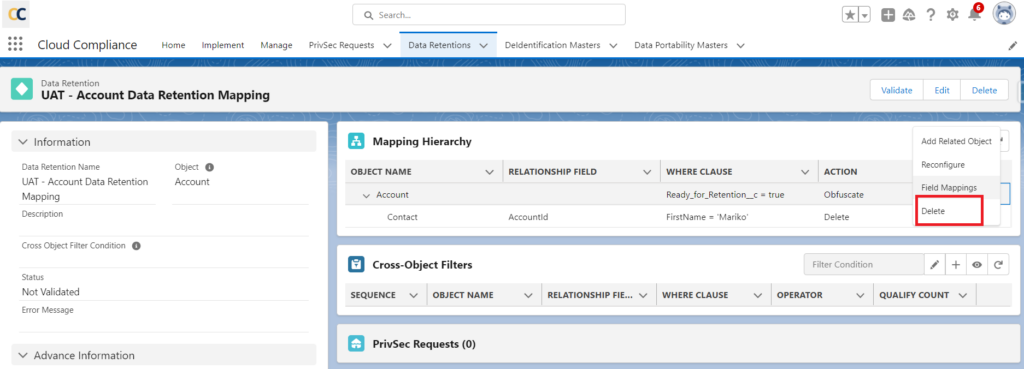
Once the Parent object gets deleted, all the child objects from the mapping get deleted.
The user cannot delete the master object which is at Level 1 as it’s a mandatory object added when a user creates a Configuration.
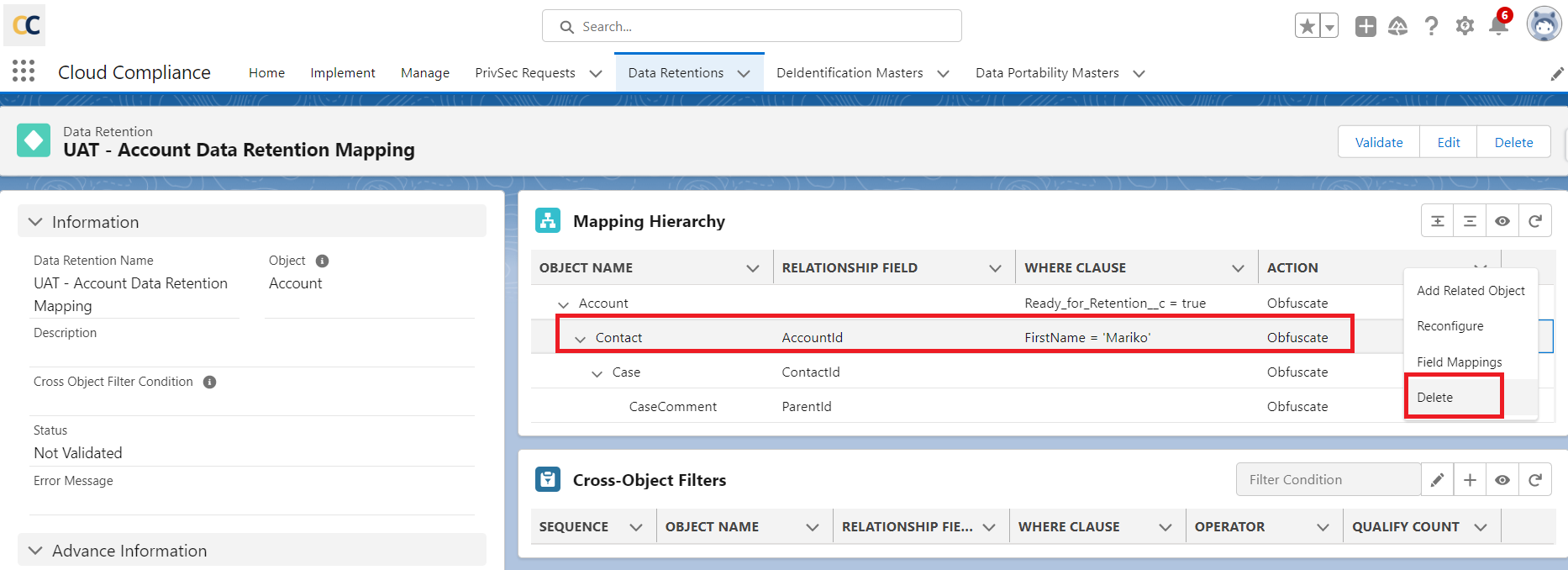
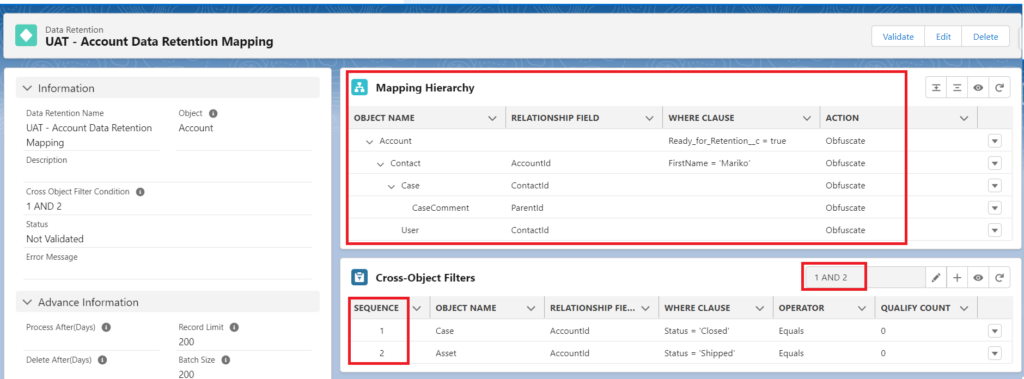
Nth level De-identification while performing Data Retention
- Nth level de-identification allows the user to de-identify/delete any number of records attached to the objects in the hierarchy mapped.
- Up to Nth levels of the hierarchy of objects can be mapped.
- Let’s add the Contact as a Level 2, Case and User objects as Level 3 objects, and CaseComment as a Level 4 object.
- Likewise, users can add as many objects to the Nth Level and add as many objects to each level.
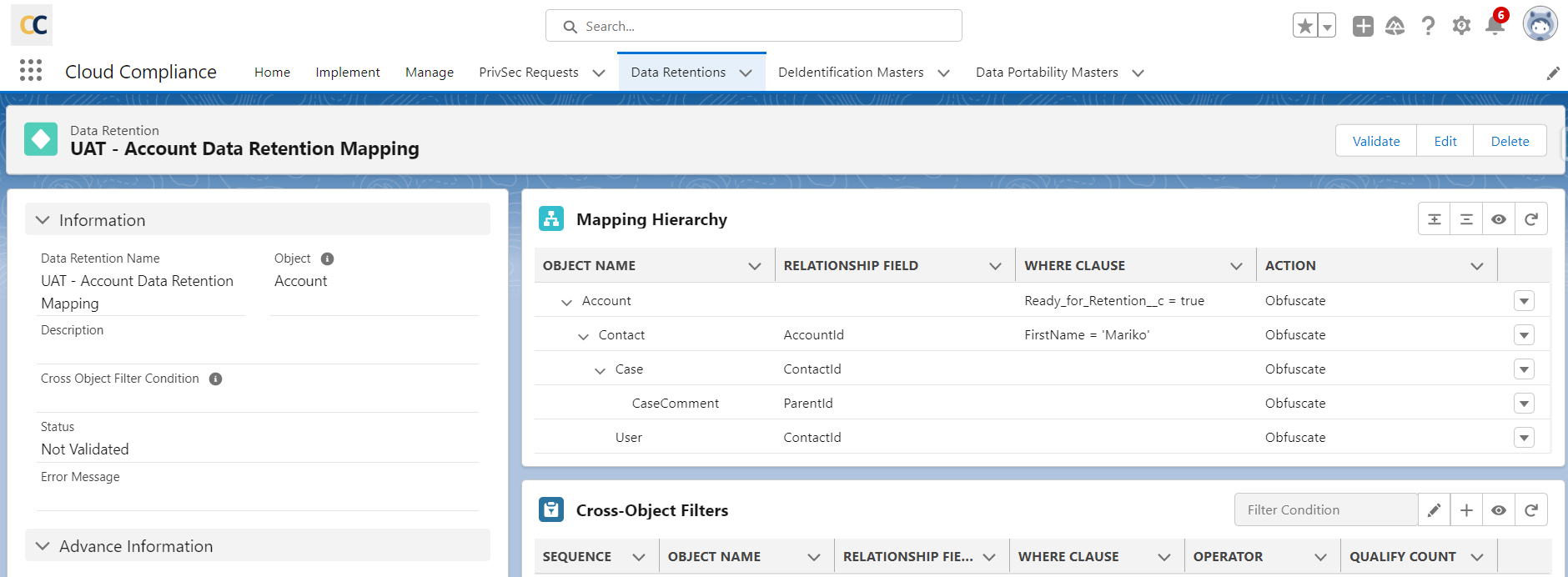
Once object mapping is ready, users can add fields to respective objects by clicking on the link ‘Field Mappings’ of each object to perform Nth Level de-identification.
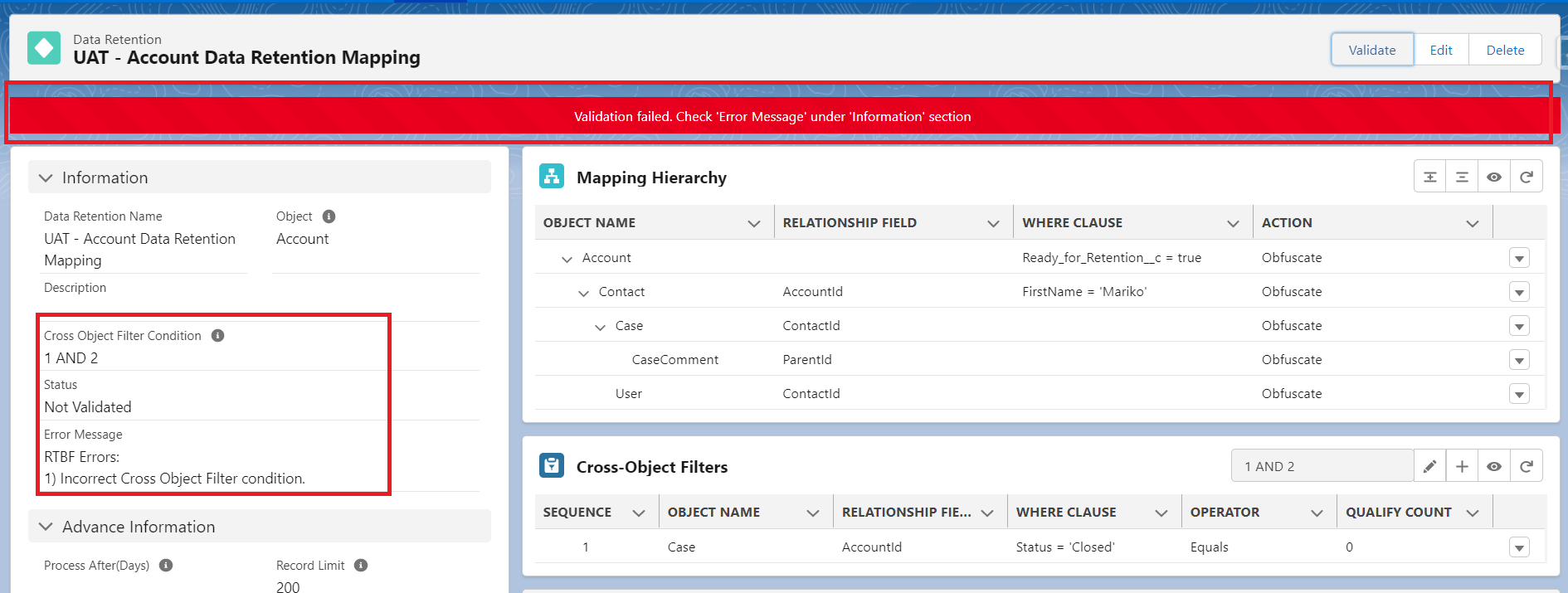
Click on the Validate button to activate the mapping.
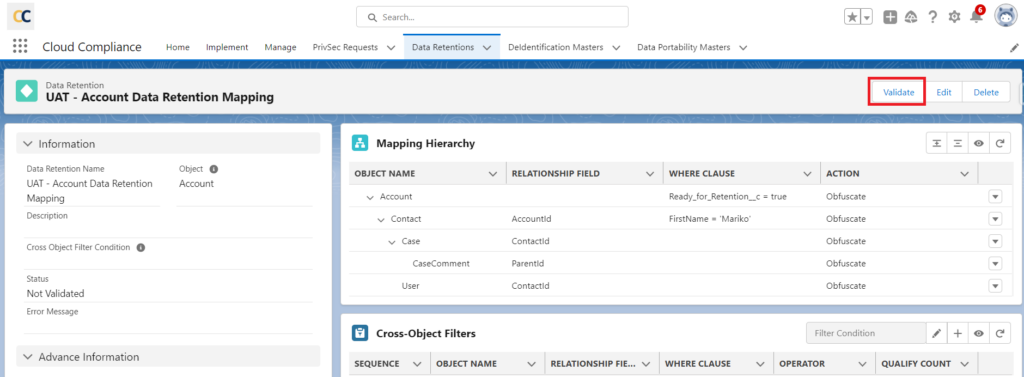
Once a user clicks on Validate button, CC will validate the mapping hierarchy, where clause and Cross Object Filters.
The ‘Error Message’ field will display if there are any errors in the Retention Rule.
In addition, a banner will be displayed on top of the page stating ‘Validation failed. Check ‘Error Message’ under the ‘Information’ section.
This will enable the user to view and rectify the errors before validating their mapping again.
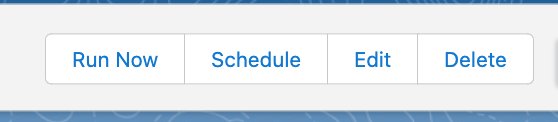
Click on ‘Validate’ again. If there are no errors then the user will see the following action buttons –
1. Run Now
2. Schedule
3. Edit
4. Delete
Users can manually run the Data Retention rule by clicking on the ‘Run Now’ button else they can schedule this mapping for a specific date and time.
In ‘Schedule’, you can schedule a Data Retention process daily, weekly, or monthly. In ‘Time’, you can provide the time at which the process needs to be scheduled for execution.
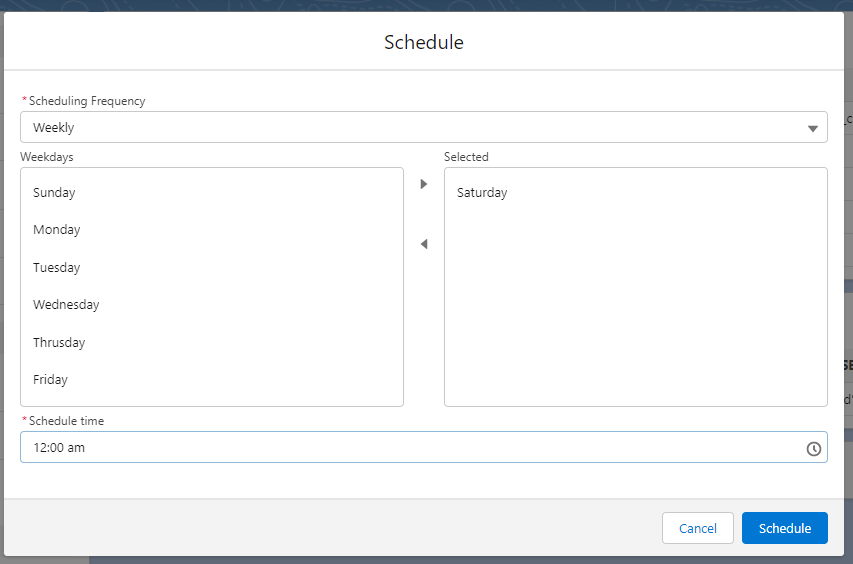
Then, click ‘Schedule’.
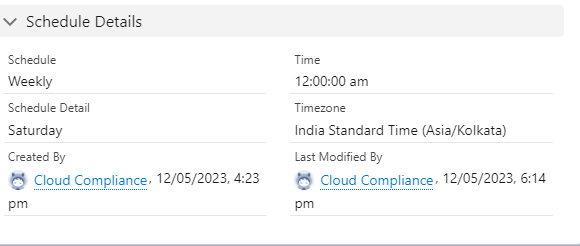
The schedule details will be visible under the Schedule Details section.
The timezone field will display the time of the scheduled retention rule based on the timezone of the user who created the Data Retention Rule.
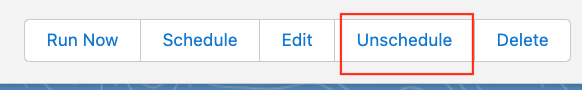
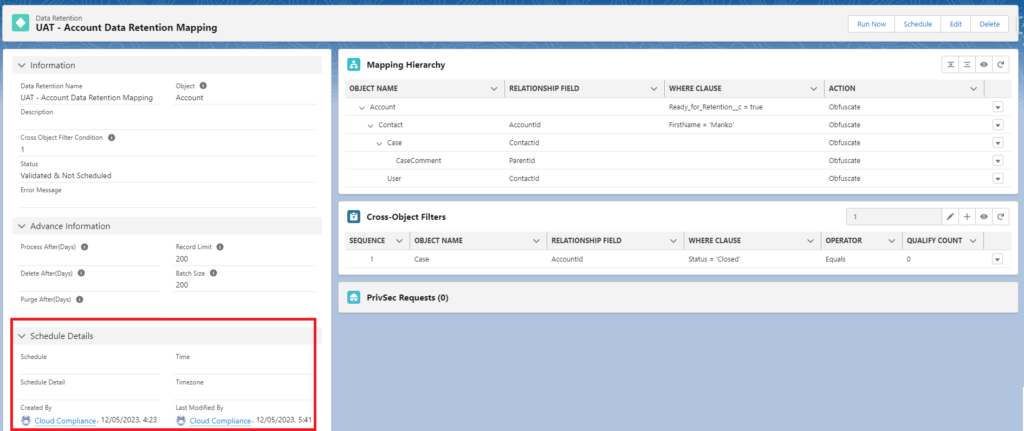
Users can click on the ‘Unschedule’ button. This action will unschedule the retention mapping and wipe out details under the ‘Schedule Details’ section.
- You can see the list of scheduled Data Retention processes.
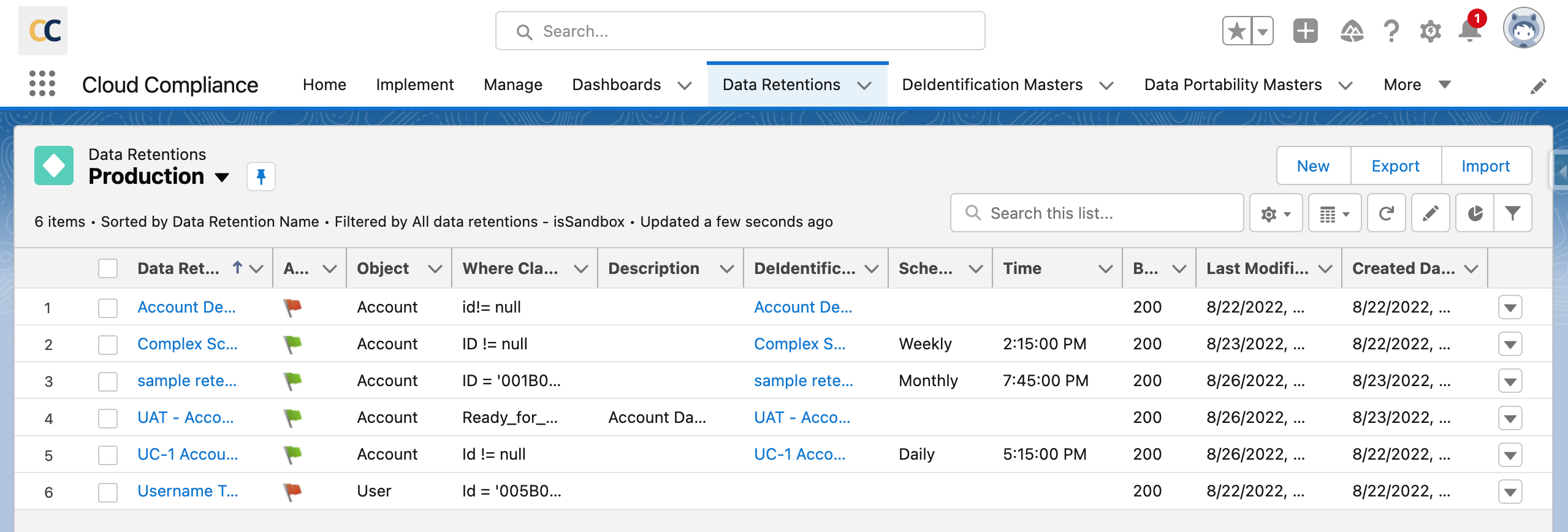
If you want to Validate and run the batch on the same instance then click on the ‘Data Retention Name’ field. This will redirect you to the detail page of specific Data Retention mapping where you will find the ‘Validate’ button. When you click on the ‘Validate’ button of the specific data retention record, the retention process will be activated and the Status field will be updated to ‘Validated’. Now you have activated your data retention rule.
Note: Whenever Process after/Delete After or Purge After field values are in the future (i.e. Not equal to 0), then the PrivSec Retention class needs to schedule.
The sample code snippet (cron job) to schedule the class daily at 1:40 AM is as follows –
PCCC_DM.PrivSecService.schedule('0 45 1 * * ?','PrivSec Scheduler');This can be executed via DevConsole