Holistically Protecting Your Salesforce Data: A Three-Bucket Strategy
Because in the realm of data security, especially concerning Salesforce, understanding the holistic approach to data protection is not just beneficial – it’s essential.

My brother and I are currently building a family house back in India (where it all began for us) and we’re at the stage where we have to decide on the wall height and gates to the house.
Up for this discussion was also, what types of doors and locks do we want to buy for the garage, main entrance and other rooms.
As simple as it may sound, the struggle to make a decision was real. Why? There were too many options – from expensive to cheap to even doing nothing!
After all who needs a gate? A gate kinda kills the aesthetics and it’s just there as a security measure. Why would someone break in? We can address it later if that actually happens anyway.
Its not a matter of if it happens but a matter of when it happens
Our home is where our heart is and where we should feel the safest at all times
The same way your CRM, Salesforce, where your customer data lies is the heart and fuel of the company and should be kept secure.
In my experience, as a Data Privacy and Security professional, I have been in many conversations where businesses acknowledge the value of securing their customer data but can’t put a number on it (ROI).
This has them postponing implementation or taking shortcuts which ends up biting them later.
In the era of GDPR, CCPA/CPRA and other country specific regulations where data privacy is at the forefront, many companies are being exposed.
If you are a CISO, Data Protection Officer, Solutions Architect or business owner who is keen to understand how to secure your Salesforce customer data, below are Salesforce Security and reference architecture options or techniques that would have you sleeping soundly at a night
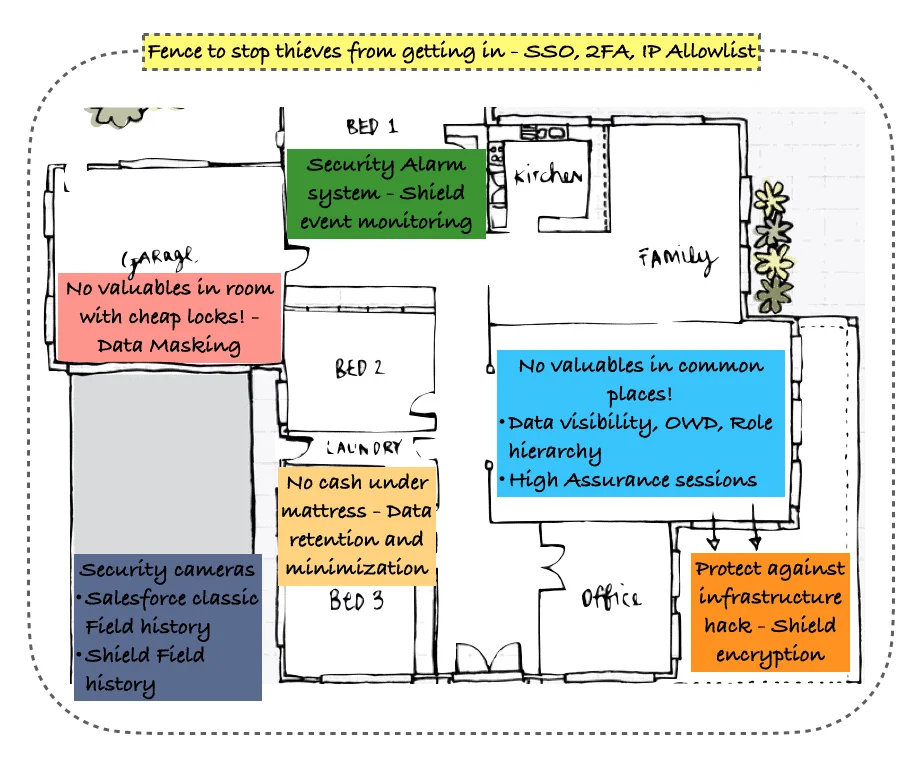
Building a fence/wall is a basic security technique that you need to have in place for your Salesforce instance.
Not having one is a signal to all sorts of hackers saying: Easy target. You don’t want to be embarrassed for doing the least.
There are 3 ways to address this:
2. Secure your valuables in the Barn – Sandbox Data Masking
You will be surprised at the number of valuables that exist in your Salesforce Sandbox.
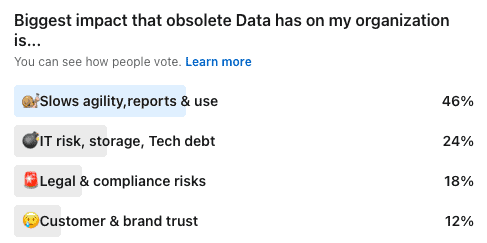
These test environments are usually exposed to third party vendors and contain sensitive customer data. I recently run a poll and was surprised at the number of people who had not noticed this was a huge security risk.
You will be surprised at the number of valuables that exist in your Salesforce Sandbox.
These test environments are usually exposed to third party vendors and contain sensitive customer data.
I recently run a poll and was surprised at the number of people who had not noticed this was a huge security risk.
A Sandbox Data Masker neutralizes those risks ad consequences of a data breach.
As mentioned, due to the sensitivity of the data on a sandbox, the data masker simply replaces the sensitive data with dummy data.
In my opinion, this is a must for every organization because NDAs don’t cut it! Money can’t be an excuse for not investing in one because there’s a free version for small businesses as well on the Salesforce AppExchange.
If your data does not possibly contribute to revenue growth, it’s not something you want to keep.
This obsolete data will never bring you a dollar in the door and your best solution is simply to reduce it. This technique is a GDPR requirement and there are SAAS products to cover this on Salesforce today
Shield Encryption is nothing but ‘security at database level’ which protects data and maintains compliance. The advantage of Shield is that it encrypts sensitive data at rest while preserving business application functionality of the org.
Two Techniques come to mind which are similar to alarm systems and security cameras in the Salesforce ecosystem. They ensure all activities are recorded and lets you know who did what, at what time. They are:
Salesforce Classic Field history– A standard feature of Salesforce which allows you to track changes on standard or custom fields on an object which can be viewed on a record’s History related list.
Shield Field Audit Trail – This is an add-on feature that lets you define a policy to retain archived field history data up to 10 years from the time the data was archived. This feature helps you comply with industry regulations related to audit capability and data retention.
Comparison of Standard Field History tracking vs Shield Field Audit Trail
Class time is over – It’s time to apply all of this theory (techniques) to your Salesforce orgs and reduce your data security vulnerabilities.
The best part is a majority of these techniques come at 0 cost and can give YOU that quick-win to keep your home safe.
An example is the FREE(Trial) Sandbox Data Masker listing on the Salesforce AppExchange. for Sandbox data masking.
The Cloud Compliance app for data retention is also available on the appexchange at affordable pricing.
For more information about Cloud Compliance visit us at: www.cloudcompliance.app and book a demo

Saurabh is an Enterprise Architect and seasoned entrepreneur spearheading a Salesforce security and AI startup with inventive contributions recognized by a patent.
Because in the realm of data security, especially concerning Salesforce, understanding the holistic approach to data protection is not just beneficial – it’s essential.

Explores how data masking is key to strengthening your Salesforce security.
Disclaimer: To all readers, please note that this not legal advice, nor is this coming from Salesforce. This is strictly my personal opinion and perspective
Marathon runners obsess over their socks and shoes – because to outdo their past performance, they need to take advantage of everything at their disposal.

Reducing Salesforce data footprint directly reduces the cost and risks of potential data leaks and embarrassment, as well as benefits your organization. Here are

We earlier talked about reducing production data. The third step to reducing data in your Salesforce org is to define retention policies. The idea here
We talked earlier about masking sandboxes. The second step is to reduce production data. The idea here is that obsolete information in your Salesforce production
Why should you mask data in Salesforce and what kind of data should you be masking to ensure security, compliance and trust. Let’s take
This website uses cookies so that we can provide you with the best user experience possible. Cookie information is stored in your browser and performs functions such as recognising you when you return to our website and helping our team to understand which sections of the website you find most interesting and useful.
Strictly Necessary Cookie should be enabled at all times so that we can save your preferences for cookie settings.
If you disable this cookie, we will not be able to save your preferences. This means that every time you visit this website you will need to enable or disable cookies again.
This website uses Google Analytics to collect anonymous information such as the number of visitors to the site, and the most popular pages.
Keeping this cookie enabled helps us to improve our website.
Please enable Strictly Necessary Cookies first so that we can save your preferences!
This website uses the following additional cookies:
Please enable Strictly Necessary Cookies first so that we can save your preferences!
More information about our Cookie Policy